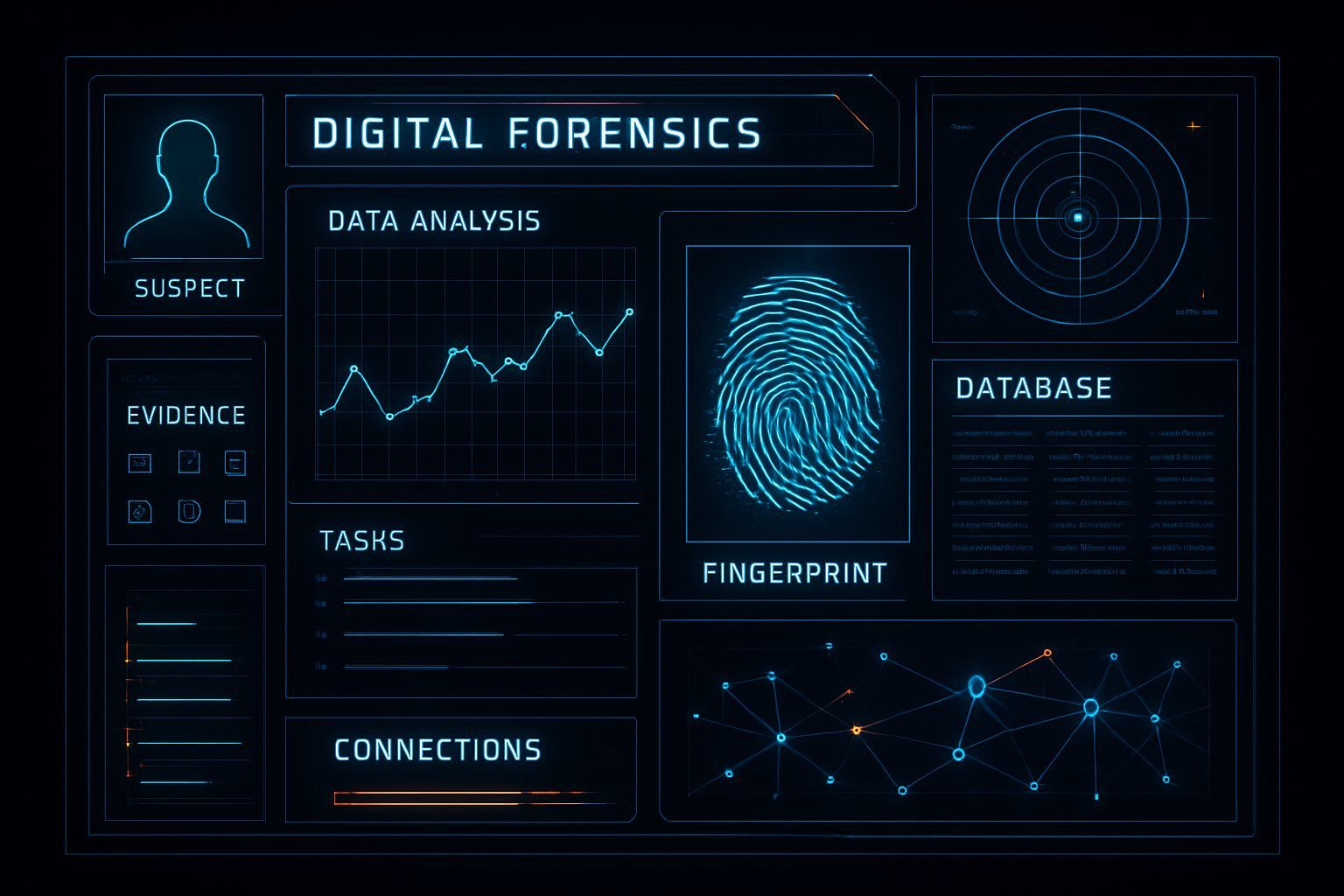
Legacy Powerhouse: Why Apple's Original AirTag Remains a Potent Tool for Cybersecurity Professionals and OSINT Researchers – Now at an Unprecedented Price Point
Explore how the AirTag Gen 1, a reliable Bluetooth tracker, offers significant value for asset tracking, digital forensics, and OSINT at an unbeatable price.