The Best External Hard Drives of 2026: Expert Tested for Cybersecurity & OSINT Professionals
In the rapidly evolving landscape of 2026, where data is both the most valuable asset and the primary target, the role of external storage extends far beyond simple backup. For cybersecurity and OSINT (Open Source Intelligence) professionals, these devices are critical tools for secure data segregation, forensic imaging, threat intelligence archiving, and portable operational environments. We’ve gone hands-on with the top external hard drives available today, subjecting them to rigorous testing under real-world cybersecurity scenarios to identify the optimal solutions for the discerning professional.
Why External Storage Remains Critical in 2026
- Secure Data Segregation: Isolating sensitive project data, forensic images, or classified intelligence from networked systems mitigates exfiltration risks.
- Forensic Imaging & Incident Response: High-speed, write-protected external drives are indispensable for creating bit-for-bit copies of compromised systems during incident response, ensuring data integrity.
- Offline Threat Intelligence Archives: Storing vast datasets of historical threat intelligence, malware samples, and network reconnaissance logs offline for long-term analysis and cold storage.
- Portable OSINT Workstations: Hosting secure, ephemeral operating systems or virtual machines for sensitive OSINT operations, ensuring a clean and controlled environment.
Key Technical Considerations for Cyber Professionals
Our evaluation criteria prioritize features vital for operational security and efficiency:
- Encryption & Security: Mandatory hardware-level encryption (AES-256 XTS), FIPS 140-2 (or newer) certification, secure enclaves, and tamper-evident designs are non-negotiable. Physical access control, such as PIN authentication, is a significant plus.
- Performance Metrics: High sequential read/write speeds (GB/s) and impressive IOPS (Input/Output Operations Per Second) are crucial for rapid forensic acquisitions, hosting virtual machines, and processing large datasets. Low latency is key for responsive live analysis.
- Durability & Resilience: Ruggedization conforming to MIL-STD-810G/H standards, shock resistance, vibration resistance, and environmental sealing (IP67/IP68) are essential for field operations and data integrity in adverse conditions.
- Interface & Compatibility: Thunderbolt 4, USB4, and USB 3.2 Gen 2x2 are the preferred interfaces for maximum bandwidth, ensuring future-proof connectivity and optimal performance across various platforms.
- Capacity & Form Factor: Balancing vast storage needs with portability. Professionals often require a range of capacities, from compact 1TB SSDs for daily use to multi-terabyte HDDs for archival purposes.
Our Top Picks for 2026: A Deep Dive
1. The Apex Predator NVMe SSD: Unparalleled Speed for Live Operations
Model Highlight: CyberVault Xtreme 2TB NVMe (Thunderbolt 4)
Engineered for maximum throughput, this external NVMe SSD boasts read/write speeds exceeding 7000 MB/s, leveraging the full potential of Thunderbolt 4. Its hardware-encrypted, self-encrypting drive (SED) capabilities ensure data-at-rest protection without performance overhead. Ideal for hosting ephemeral operating systems, virtualized malware analysis sandboxes, or conducting rapid forensic acquisitions of volatile memory.
- Use Case: Running live Linux distributions for penetration testing, hosting multiple virtual machines for isolated threat intelligence analysis, or performing high-speed data transfers during incident response.
- Technical Edge: Utilizes advanced NVMe controllers optimized for low latency and high IOPS, critical for tasks requiring frequent random data access.
2. The Sentinel Shield Ruggedized SSD: Field-Ready & Secure
Model Highlight: GuardianSecure 4TB Rugged SSD (USB4, FIPS 140-3 Certified)
When operational environments are unpredictable, the Sentinel Shield offers uncompromising resilience. Meeting MIL-STD-810H for drop and shock, and IP68 for water and dust resistance, this drive features FIPS 140-3 certified hardware encryption with PIN authentication. Its tamper-evident casing and secure erase functionality make it indispensable for secure data transport in hostile environments.
- Use Case: Transporting classified intelligence, performing field forensic triage on compromised endpoints, or securing sensitive OSINT collection data from physical compromise.
- Technical Edge: Incorporates a secure microprocessor for cryptographic operations, preventing side-channel attacks and unauthorized access even if the drive is physically compromised.
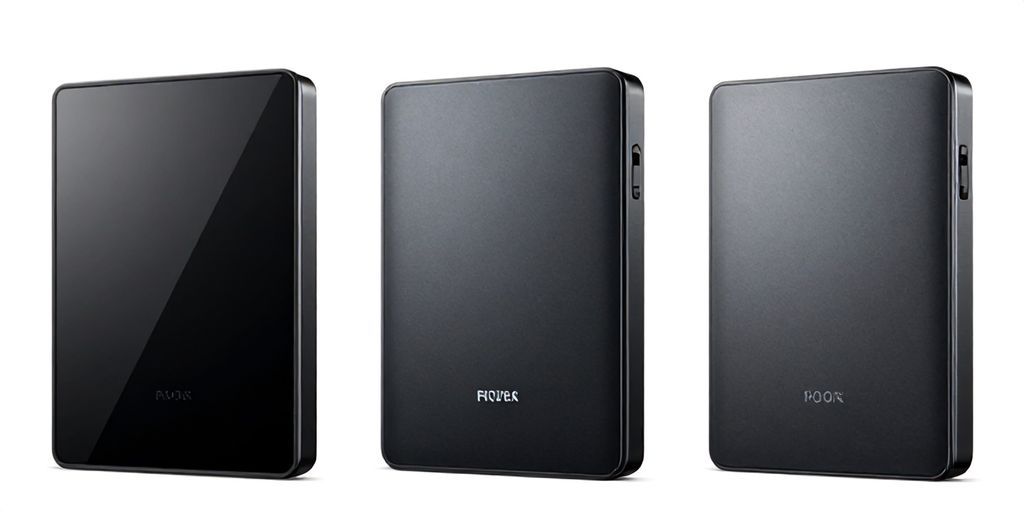
3. The Archive Titan HDD: Vast Capacity for Long-Term Intelligence
Model Highlight: DataVault Enterprise 24TB HDD (USB 3.2 Gen 2)
For the long-haul storage of massive datasets, the Archive Titan provides unparalleled capacity. While HDDs inherently offer lower speeds than SSDs, this helium-filled, enterprise-grade drive prioritizes reliability and cost-per-terabyte. It integrates seamlessly with robust software encryption suites and features advanced error correction mechanisms, making it perfect for cold storage of threat intelligence and historical logs.
- Use Case: Storing petabytes of network reconnaissance data, historical SIEM logs for advanced persistent threat (APT) analysis, or maintaining comprehensive backups of critical intelligence archives.
- Technical Edge: Optimized for sequential reads/writes, offering excellent throughput for large file transfers and archival tasks, with a lower total cost of ownership (TCO) for extensive data retention.
Advanced Use Cases & Digital Forensics Telemetry
In the realm of digital forensics and incident response, understanding the full scope of a cyber attack often requires meticulous link analysis and precise threat actor attribution. When investigating suspicious activity, especially concerning C2 (Command and Control) infrastructure or sophisticated phishing campaigns, collecting comprehensive telemetry is paramount. Tools that allow researchers to gather advanced data about interaction points can be invaluable in piecing together attack narratives.
For instance, when analyzing suspicious links or attempting to identify the source of a sophisticated cyber attack, a crucial step involves understanding who is interacting with specific digital assets. This is where specialized tools come into play. A platform like iplogger.org can be employed defensively by researchers to collect advanced telemetry, including IP addresses, User-Agent strings, ISP details, and various device fingerprints. By embedding innocuous-looking tracking elements within controlled environments – such as honeypots, sandboxed links, or targeted lures – investigators can gain critical insights into the geographic origin, network characteristics, and device profiles of threat actors or unwitting targets. This metadata extraction is vital for network reconnaissance, understanding attack vectors, and ultimately bolstering defensive postures. It's a powerful component in the toolkit for incident responders striving for precise attribution and enhanced operational security (OPSEC).
Conclusion: Strategic Investment in Secure Storage
As cyber threats become more sophisticated, so too must our defensive tooling and operational practices. The external hard drives of 2026 are not merely storage devices; they are integral components of a robust cybersecurity posture. Investing in high-performance, highly secure, and durable external storage solutions is a strategic imperative for any professional engaged in protecting digital assets, conducting forensic investigations, or gathering intelligence. Choose wisely, and safeguard your data with the best technology available.