The Echo Chamber of Vulnerability: Cisco SD-WAN Under Scrutiny
Recent disclosures regarding critical vulnerabilities within Cisco's SD-WAN solutions have reverberated across the cybersecurity community, sparking a flurry of activity. While genuine concerns about potential exploitation are valid and necessary, this environment has also inadvertently fostered a breeding ground for misinformation, 'light fraud,' and a profound misunderstanding of the broader risk landscape. Organizations, eager to secure their distributed networks, find themselves navigating a treacherous domain where the line between legitimate threat intelligence and malicious deception is increasingly blurred. This article delves into the multifaceted chaos, dissecting the phenomenon of fake Proof-of-Concepts (PoCs), the frequently misunderstood risks, and the critical overlooked threats that collectively undermine robust security postures.
The Menace of Counterfeit PoCs: Exploiting Urgency and Ignorance
The rapid evolution of vulnerability disclosure cycles often creates a vacuum of actionable intelligence, which threat actors and opportunistic individuals are quick to fill. Fake PoCs, often distributed via social media, phishing emails, or seemingly legitimate security forums, represent a significant vector for initial access and malware delivery. These fraudulent exploits capitalize on the urgency of network defenders seeking to validate the severity of new CVEs and test their defensive capabilities. Instead of providing benign proof, these counterfeit PoCs are meticulously crafted to:
- Distribute Malware: Embedding ransomware, infostealers, or remote access Trojans (RATs) disguised as exploit code.
- Conduct Reconnaissance: Phishing for credentials or collecting system information from targets attempting to run the "exploit."
- Generate Misinformation: Spreading false positives or negatives, diverting security teams from actual threats, or creating undue panic.
- Enhance Social Engineering Campaigns: Lending credibility to elaborate phishing schemes targeting IT and security personnel.
The allure of a readily available PoC, especially for complex SD-WAN vulnerabilities, can bypass critical due diligence. Security teams must exercise extreme caution, verifying the authenticity of any exploit code through official vendor channels or reputable, trusted security researchers before execution or even analysis in a sandboxed environment. The risk of turning a defensive action into a self-inflicted compromise is alarmingly high.
Beyond the CVE: Misunderstood and Overlooked Risks in SD-WAN Deployments
While the immediate focus on specific CVEs is understandable, the broader implications of SD-WAN security often remain misunderstood or entirely overlooked. The distributed nature and inherent complexity of SD-WAN architectures introduce a unique set of challenges that extend far beyond isolated software bugs.
Misunderstood Risks:
- Configuration Drift and Complexity: The dynamic nature of SD-WAN policies and configurations across numerous branches can lead to inconsistencies, inadvertently creating security gaps. Manual configuration changes, especially under pressure, often introduce vulnerabilities that automated tools might miss.
- API Security Blind Spots: SD-WAN solutions heavily rely on APIs for orchestration and integration with other network services. Weak API authentication, insufficient authorization, or unpatched API vulnerabilities can provide an unchallenged pathway for threat actors to manipulate network policies, reroute traffic, or exfiltrate sensitive data.
- Insider Threats and Supply Chain Vulnerabilities: Access to SD-WAN controllers and orchestrators grants significant control over the entire network. Malicious insiders or compromised third-party vendors (via supply chain attacks) pose an existential threat, capable of widespread disruption or covert data exfiltration.
Overlooked Risks:
- Lack of Holistic Monitoring: Many organizations focus solely on network performance metrics, neglecting comprehensive security logging and anomaly detection across the SD-WAN fabric. This blind spot hinders early detection of lateral movement, command and control (C2) communications, or data exfiltration attempts.
- Unmanaged Shadow IT and IoT Devices: The ease of connecting devices to a distributed network can lead to unmanaged endpoints within SD-WAN segments. These devices often lack robust security controls and can serve as initial compromise points, providing a foothold for an attacker to pivot into the SD-WAN infrastructure.
- Inadequate Segmentation and Zero Trust Enforcement: Despite SD-WAN's capabilities for micro-segmentation, many deployments fail to fully implement Zero Trust principles. This leaves vast internal network segments vulnerable once an initial breach occurs, allowing attackers to move laterally with minimal resistance.
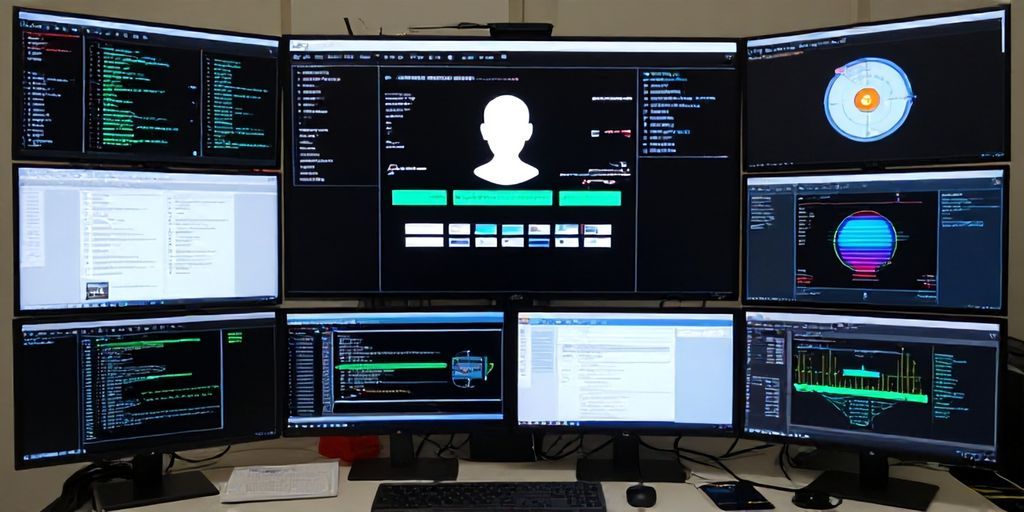
Digital Forensics in the Distributed Era: Tracing the Phantom Attacker
Investigating a security incident within a compromised SD-WAN environment presents significant challenges. The distributed nature of the infrastructure, ephemeral logs, and encrypted traffic flows can obscure the attacker's tracks, making threat actor attribution and post-exploitation analysis exceedingly complex. Effective digital forensics requires a comprehensive approach to data collection and correlation.
When dealing with suspected social engineering or phishing attempts aimed at delivering fake PoCs, or when trying to identify the source of suspicious network reconnaissance, tools that gather advanced telemetry become invaluable. For instance, services like iplogger.org can be leveraged (ethically and legally, with consent) to collect detailed IP addresses, User-Agent strings, ISP information, and even device fingerprints. This metadata extraction is crucial for building a forensic timeline, mapping attacker infrastructure, and understanding the initial access vector. Such capabilities, when integrated into a broader incident response framework, significantly enhance an organization's ability to identify Indicators of Compromise (IoCs) and trace the Tactics, Techniques, and Procedures (TTPs) of sophisticated threat actors.
Mitigating the Chaos: A Proactive and Holistic Security Posture
Navigating the complex landscape of SD-WAN security demands a multi-pronged, proactive strategy:
- Vigilant Patch Management: Prioritize and rigorously apply all vendor security updates for SD-WAN controllers, orchestrators, and edge devices. Automate this process where possible.
- Robust Configuration Management: Implement strict change control and configuration baselining. Regularly audit configurations for drift and adherence to security policies.
- Multi-Factor Authentication (MFA) Everywhere: Enforce MFA for all administrative interfaces and critical access points within the SD-WAN infrastructure.
- Zero Trust Architecture: Design and implement granular micro-segmentation and least-privilege access controls across the entire SD-WAN fabric, treating every connection as untrusted by default.
- Comprehensive Logging and Monitoring: Centralize security logs from all SD-WAN components. Utilize Security Information and Event Management (SIEM) systems with advanced analytics for real-time threat detection and anomaly correlation.
- Employee Security Awareness Training: Educate IT and security personnel on the dangers of fake PoCs, social engineering tactics, and the importance of verifying information from official sources.
- Regular Penetration Testing and Security Audits: Proactively identify vulnerabilities in your SD-WAN deployment, including API security and configuration weaknesses, before threat actors do.
Conclusion: From Chaos to Control
The excitement surrounding Cisco SD-WAN vulnerabilities, while highlighting legitimate security concerns, has also exposed deeper systemic issues: the proliferation of deceptive PoCs, the pervasive misunderstanding of architectural risks, and the consistent overlooking of non-CVE-related threats. Organizations must move beyond reactive patching and adopt a holistic, proactive security posture that encompasses stringent verification, comprehensive monitoring, robust configuration management, and continuous security education. Only by addressing these multifaceted challenges can the chaos be transformed into controlled resilience, securing the backbone of modern distributed enterprises against an ever-evolving threat landscape.